
IT Security Assessment Report
Though IT security has always been a critical component of a complete business strategy, it should be the primary focus of today’s IT efforts for forward-thinking organizations. IT security assessments aim to reveal system weaknesses to help firms evaluate and manage their risk.
In the past, IT security assessments were straightforward, looking at fundamentals like user activity and authorizations. While these are still vital factors for your business to track, a solid cybersecurity strategy does not end there.
If your current IT services are similar to what we just described, you might wonder what an IT security assessment report should look like. Keep reading as we explore the components a thorough evaluation includes.
Table of Contents
- What Is an IT Security Assessment Report?
- Types of IT Security Assessments
- Components of an IT Security Assessment Report
- What to Do With Your Assessment
What Is an IT Security Assessment Report?
Modern-day IT security assessments follow very different guidelines from those of their dated counterparts. You expect your outsourced managed IT support company to identify critical flaws and loopholes and proactively patch them before a data breach. Most of today’s companies connect to millions of customers online, giving hackers and other online threats more entry points to attack.
Following the correct IT security assessment procedures should be at the top of your priority list. Proper security measures can prevent unauthorized users from exploiting your vulnerabilities while still allowing access to clients. The managed security professionals you hire should perform regular assessments, reviews and audits to facilitate this.
Types of IT Security Assessments
Anything that can disrupt your firm’s daily operations falls under the umbrella of items to evaluate. Let’s review some security assessments a managed IT support company can perform.
Vulnerability Assessment
A vulnerability assessment identifies weaknesses within your business applications, network or system. Each system or software upgrade, new feature or code update exposes your IT systems to new risks that did not exist during your initial scan. Vulnerability assessments should be ongoing to minimize vulnerabilities presented by the upgrades and additions.
Penetration Testing
The goal of penetration testing is similar to that of a vulnerability assessment. However, the techniques used in each are very different. Your managed IT support company completes penetration testing by serving as ethical hackers. Their mission is to mimic a cybercriminal’s activity, including stealing sensitive customer information. The reports produced by this testing give your organization insight into where it is most susceptible and what you can fix.
Risk Assessment
A risk assessment determines the acceptable risk for your firm. It essentially lists all possible cyberthreats at various severity levels, checks the likelihood that these attacks will happen and measures their potential impact.
Components of an IT Security Assessment Report
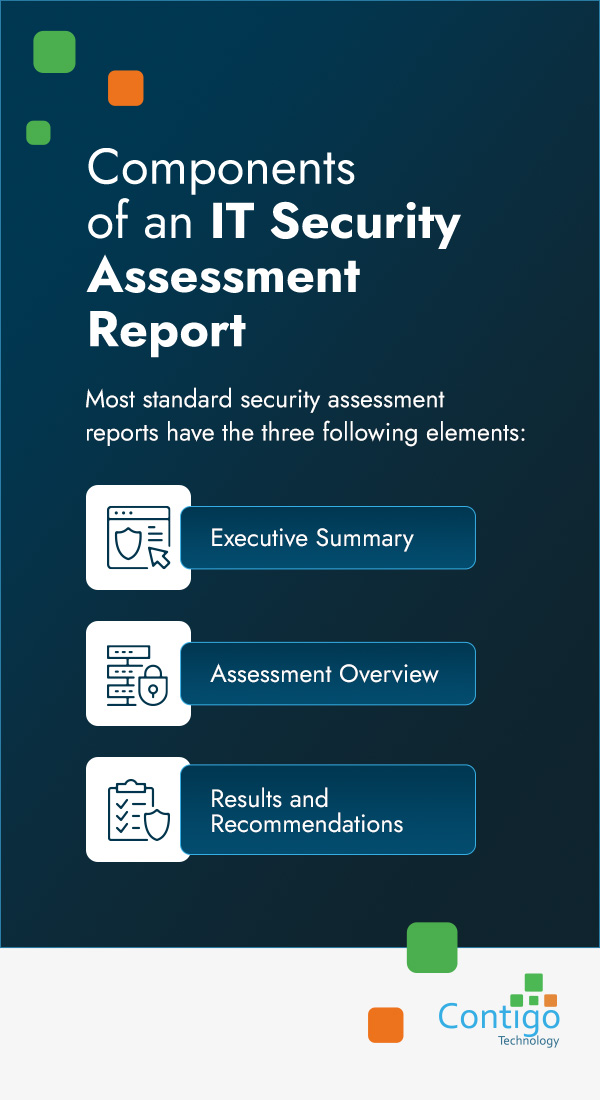
An IT security assessment report usually includes background information, objectives and limitations regarding your IT system’s security. It should detail the current IT environment, describing the examination methods and the tools and equipment used to conduct the assessment.
The summary should contain the overall findings from the testing. Besides these items, your information security assessment report must also list detailed data on the results achieved for the various tests, with pertinent drawings and diagrams. It should end with recommendations and a final analysis based on the test results and findings.
Most standard security assessment reports have the three following elements.
Executive Summary
The executive summary is an overview of the assessment’s findings. It gives enterprises a quick idea of how well or poorly their systems and applications performed by highlighting the severity and number of risks identified during the scan. This section provides a big-picture look at the overall state of an organization’s IT security, letting business leaders and managers prioritize their cybersecurity efforts accordingly.
Assessment Overview
The assessment overview outlines the methods, tools and basis for the approach used in the analysis. This portion gives companies more insight into how their IT provider reached its conclusion and ensures the legitimacy of the results.
Results and Recommendations
The results and recommendations section is vital to an IT security risk assessment report. In this segment, you can expect to see a description of each detected vulnerability, including what caused it, its severity and a recommendation on how to fix it. The high level of detail in this section is crucial for helping organizations develop a strong course of action to address their existing network’s security problems.
What to Do With Your Assessment

Performing a thorough assessment is an excellent start to improving your enterprise’s cybersecurity, but you won’t gain from it unless you act on the findings. While security assessments are part of some sectors’ compliance initiatives, you can do so much more with this information than merely fulfilling your legal obligations.
Take the following measures after receiving your results to take full advantage of your security assessment.
- Distribute the findings throughout the chain of command: It can be challenging to digest the results of a security assessment alone. Plus, you will likely need your boss’ approval to address some aspects.
- Use recommendations to your advantage: Your security risk assessment report will provide in-depth suggestions. After reviewing these, you should create a timeline with well-defined steps for fixing, mitigating or accepting the risks associated with each weak point. Remember, the idea is to work on proactively reducing your risk to prevent malicious actors from exploiting your system’s vulnerabilities, so don’t wait too long to formulate a plan and act on it.
- Continue to use a consistent assessment methodology for tracking: Keeping your testing methods and risk register format allows your organization to appropriately prioritize each issue’s importance. Additionally, it helps firms track their risk mitigation progress over time.
Contact Contigo Technology for a Complimentary Network Assessment
An IT security assessment is a fundamental way to fight cyberthreats and protect your company’s sensitive data. These evaluations can significantly decrease external attacks, making them crucial for maintaining a healthy network. In addition, performing these tests can create awareness within your firm, minimizing potential internal threats.
Contact us to partner with a managed service provider that specializes in going the extra mile for security. At Contigo Technology, we provide the best technical support possible to protect your business from cybersecurity threats and attacks. Our reporting services can even offer insight into the measures we take to keep you secure.

